Accessibility Options : access.cpl
Add Hardware : hdwwiz.cpl
Add / Remove Programs : appwiz.cpl
Administrative Tools : control admintools
Automatic Updates : wuaucpl.cpl
Wizard file transfer Bluethooth : fsquirt
Calculator : calc
Certificate Manager : certmgr.msc
Character : charmap
Checking disk : chkdsk
Manager of the album (clipboard) : clipbrd
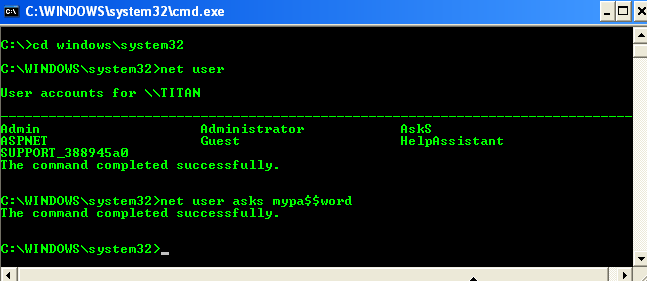
Command Prompt : cmd
Service components (DCOM) : dcomcnfg
Computer Management : compmgmt.msc
DDE active sharing : ddeshare
Device Manager : devmgmt.msc
DirectX Control Panel (if installed) : directx.cpl
DirectX Diagnostic Utility : dxdiag
Disk Cleanup : cleanmgr
System Information : dxdiag
Disk Defragmenter : dfrg.msc
Disk Management : diskmgmt.msc
Partition manager : diskpart
Display Properties : control desktop
Properties of the display (2) : desk.cpl
Properties display (tab "appearance") : control color
Dr. Watson : drwtsn32
Manager vérirficateur drivers : check
Event Viewer : Eventvwr.msc
Verification of signatures of files : sigverif
Findfast (if present) : findfast.cpl
Folder Options : control folders
Fonts (fonts) : control fonts
Fonts folder windows : fonts
Free Cell : freecell
Game Controllers : Joy.cpl
Group Policy (XP Pro) : gpedit.msc
Hearts (card game) : mshearts
IExpress (file generator. Cab) : IExpress
Indexing Service (if not disabled) : ciadv.msc
Internet Properties : inetcpl.cpl
IPConfig (display configuration) : ipconfig / all
IPConfig (displays the contents of the DNS cache) : ipconfig / displaydns
IPConfig (erases the contents of the DNS cache) : ipconfig / flushdns
IPConfig (IP configuration cancels maps) : ipconfig / release
IPConfig (renew IP configuration maps) : ipconfig / renew
Java Control Panel (if present) : jpicpl32.cpl
Java Control Panel (if present) : javaws
Keyboard Properties : control keyboard
Local Security Settings : secpol.msc
Local Users and Groups : lusrmgr.msc
Logout : logoff
Microsoft Chat : winchat
Minesweeper (game) : winmine
Properties of the mouse : control mouse
Properties of the mouse (2) : main.cpl
Network Connections : control NetConnect
Network Connections (2) : ncpa.cpl
Network configuration wizard : netsetup.cpl
Notepad : notepad
NView Desktop Manager (if installed) : nvtuicpl.cpl
Manager links : packager
Data Source Administrator ODBC : odbccp32.cpl
Screen Keyboard : OSK
AC3 Filter (if installed) : ac3filter.cpl
Password manager (if present) : Password.cpl
Monitor performance : perfmon.msc
Monitor performance (2) : perfmon
Dialing Properties (phone) : telephon.cpl
Power Options : powercfg.cpl
Printers and Faxes : control printers
Private Character Editor : eudcedit
Quicktime (if installed) : QuickTime.cpl
Regional and Language Options : intl.cpl
Editor of the registry : regedit
Remote desktop connection : mstsc
Removable Storage : ntmsmgr.msc
requests the operator to removable storage : ntmsoprq.msc
RSoP (traduction. ..) (XP Pro) : rsop.msc
Scanners and Cameras : sticpl.cpl
Scheduled Tasks : control schedtasks
Security Center : wscui.cpl
Console management services : services.msc
shared folders : fsmgmt.msc
Turn off windows : shutdown
Sounds and Audio Devices : mmsys.cpl
Spider (card game) : spider
Client Network Utility SQL server : cliconfg
System Configuration Editor : sysedit
System Configuration Utility : msconfig
System File Checker (SFC =) (Scan Now) : sfc / scannow
SFC (Scan next startup) : sfc / scanonce
SFC (Scan each démarraget) : sfc / scanboot
SFC (back to default settings) : sfc / revert
SFC (purge cache files) : sfc / purgecache
SFC (define size CAHC x) : sfc / cachesize = x
System Properties : sysdm.cpl
Task Manager : taskmgr